This is a really cool tool to test how good your password would hold up to a brute-force attack:
https://www.grc.com/haystack.htm
Also, this sums things up:

When I unboxed my Microsoft Band, it had an 80% charge. I slept with it that night, and it was at 80% in the morning. I threw it on the charger for 30 minutes while I showered, and it was still at 80%. It seems like it really likes 80%!
I wore it that day and slept with it again and it was still looking like the battery was near the top, so I decided not to charge it in the morning while I showered to see how long it would go. I wore it that day, and slept with it again. It stopped recoding my sleep about 3am.
So I put it on a charge at 6am when I got up, and 2 hours later when I checked, it was at 80%. 80% again. I was wondering if it even had 100% as a charge metric. But, 15 minutes later, I finally got to see 100% charge. Now that it is fully charged, I’ll see how long I can wear it before it dies. I suspect that it will 2 full days and nights. But even if it doesn’t, it certainly can handle 1 full day without issue. Not bad at all!
Admittedly this is probably not a big problem for most people, but if you find that pulling your phone out at inopportune moments has caused you disaster, then the Microsoft Band may be for you. I know someone who accidentally dropped their phone into a flushing toilet! I had a phone slip from its holster, noiselessly through the gap in-between an elevator and the floor, taking a 4 story plunge to its death. Both of these scenarios could have been avoided if our phones were safely tucked away because we could monitor the majority of our communications with Microsoft Band.
I just purchased one so I will be posting about it as I learn how it works. So far, I really like it. Here is my first impressions so far.
Although it looks like a shackle, as Paul Thurrott mentioned in a recent podcast, it fits surprisingly well and is very comfortable. I wore it last night and it provided some very illuminating information about my sleep.
Today, I have been using it to stay on top of my email which has been amazing. I hadn’t realized just how much work it is to take my phone out of its holster or my pocket. That sure sounds lazy! Still, I find I really like doing it that way. Perhaps it will get old. We’ll see.
I also did a couple workouts and it kicked my butt! I would like to see an integration with the service I use at the YMCA which builds workouts which I can print out and follow (e.g. Leg press, 200lbs, 12 reps, rest 60 sec, etc.). The band would be perfect for this. Perhaps that’s what the Golds Gym workouts do as I have not looked at them yet.
So far, I’m very happy I steelhead out the $200. Lets see how I feel about that in a week.
I stumbled upon the coolest web form creator called TypeForm. It users interactive imagery to convey a deeper tie between the form and it’s purpose. One great example is a form asking for ones age could display a birthday cake which changes the candles based on the answer, then blows them out. Very cool. I cann’t wait to try it out. Find it at http://www.typeform.com
The Riverbed SteelHeads (SH) is a platform that, simply said, speeds up connections across the wide-area network (WAN). Riverbed solutions improve network performance and thus user satisfaction and productivity, enable storage and server consolidation into the data center by making application performance across the WAN feel like the server or storage is still local in the remote office, and provide a visualization platform for applications needing to remain in the remote office while still being managed centrally, all while lowering ongoing operating expenses by avoiding bandwidth upgrades and requiring fewer managed devices.
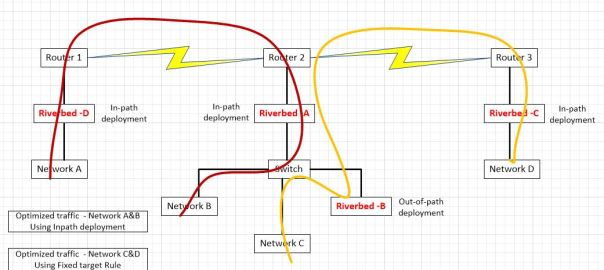
One Riverbed customer had a question about how they could integrate two Riverbed optimized networks; one they control (A&B) and another, the do not (C&D). They desired to keep the Riverbeds from each set of networks separate. My response was posted to a technical forum but I also include it here since I found it very interesting. It assumes technical proficiency with the Riverbed SteelHead platform, so unfortunately it will not be appropriate read for those not familiar with the workings of the product.
Using their diagram, let’s take a look at some of the technical requirement around how this would work:
In this scenario, networks A and B are optimizing via auto-discovery by Riverbed A and Riverbed D. Networks C and D are being optimized by a fixed-target rule on Riverbed C pointing to the out-of-path Riverbed B. The question was asked, if we don’t control networks C and D, what needs to be done to ensure that Riverbed A does not participate in optimization between network C and D.
If optimization is indeed occurring between clients on network D and servers on network C via a fixed target rule on Riverbed C pointing to Riverbed B, no peering rule is necessary on Riverbed A to avoid participation in optimization since peering rules are not invoked unless an auto-discovery probe is received. Fixed-Target rules do not initiate such an auto-discovery probe since fixed-target rules hard code the Riverbed to peer with. Furthermore, the optimized connection created by that fixed target rule from Riverbed C to Riverbed B is made on TCP port 7810 which is included in the default pass-through rules on Riverbed A for Riverbed protocols.
However, if we want to make sure that Riverbed C never peers with Riverbed A (due to sizing constraints for example), since both are in-path and may auto-discover each other, we will need both a peering rule and an in-path rule on Riverbed A. Riverbed C may be configured not to perform auto-discovery, but unless we have visibility into its configuration, you can’t be sure.
To handle inbound connections from network D to network C, we would put a peering rule on Riverbed A, matching Riverbed C’s in-path IP address. This ensures that a connection coming from a client on network D to a server on networks B or C would not be optimized. In essence, the peering rule on Riverbed A says to not respond to auto-discovery probes from Riverbed C for any networks behind it. We can also be more selective in the peering rule by using networks’ subnets instead of a peer IP. For example, we could allow connections from clients on network D to be optimized (by Riverbed C and Riverbed A auto-peering) for network B but not network C. We can think of a peering rule as answering the question, “what do I do when I receive an auto-discovery probe from another Riverbed?” If we don’t want optimization from network D to network C, but we do want optimization from network A to network C, the peering rule on Riverbed A would be specific to a peer IP address of Riverbed C. If we don’t want anyone auto-peering with Riverbed A when going to network C, the peering rule would use a destination subnet of network C.
Now, for outbound connections being initiated by clients on network C, due to the way server-side out-of-path works, outbound connections from network C will never be seen by Riverbed B. However, they will be seen by the in-path Riverbed A and thus will receive an auto-discovery probe. Other Riverbeds will respond to that probe and thus cause those connections to be optimized. So, for a connection being initiated on network C going to network D, a probe would be generated by Riverbed A and that probe would then be seen by Riverbed C and they would optimize that connection. Thus, if we don’t want Riverbed A and Riverbed C peering up for connections from network C to network D, we must put an in-path rule on Riverbed A to pass-through connections from network C to network D. If we don’t want Riverbed A optimizing any outbound connections from network C, that in-path rule would just match the source address of network C.
In summary, if we are just trying to keep Riverbed A from peering with Riverbed C, all we need is:
This scenario still allows optimized connections from network A to network C or from network D to network A.
If we are instead trying to prohibit all optimization when networks A or B communicate with networks C or D, it is a little more complex. To do that we need:
Today, I decided I would just take a picture of our church choir schedule so I would have it on my phone for reference. I remembered that Paul Thurrott on his Windows weekly podcast mentioned that the latest Microsoft Lens app could do Optical Character Recognition (OCR) and put the text and/or the image in OneNote. So I tried it. Wow! It works great!
After opening the app, I snapped a picture. The first cool thing was that it corrected for the angle from which I took the picture so the page looked as if I snapped the picture squarely from the front. I then told it I wanted a word doc and to store the pic in OneNote. I chose to share a link to the doc with a friend and sent it to myself. I opened the .docx file on my windows phone and could see the text converted from the image right above the picture so it was easy to compare to make sure it did it correctly. It did. I love it when technology foes exactly what I want it to do.
Google Glass is great idea. The idea of having an always-on link to your Personal Digital Assistance (PDA) is appealing. Unfortunately, the execution in Google Glass leaves a lot to be desired. For starters, it’s too distracting, both to the user and those around them. Questions arise such as “Is there wearer giving me their full attention?” and “Are they recording our conversation?” Data input is also a challenge since voice is the only real way to interact with Google Glass and unfortunately, the voice recognition is lacking, not to mention the challenges of a noisy environment. Also, let’s face it. They just look silly. I’d certainly consider wearing them when you can get them as contacts or seamlessly built into a pair of Ray-bans, but not as they exist today. So if Google Glass misses the mark, what kinds of things am I looking for in a PDA?
I think that the Perfect Personal Digital Assistant (PPDA?) is one that is there when I need it, not distracting, and invisible the rest of the time (unlike Google Glass). It should use available information to predict my needs and be available to answer any question I might have. Here are some of the attributes the perfect PDA should have:
I’ve used a number of examples of how my Windows Phone meets my criteria in what I’m looking for. It’s the closest thing I’ve found. But it is still a long way from being the Perfect PDA. Technology advancements in CPU, memory, and battery life will be necessary to bring my PPDA to life. But I expect I will see it in a few short years. I can’t wait to post my first blog entry entirely dictated, edited, and posted using my PPDA. Is that so much to ask?
 I found a company called Incapsula that is able to easily front-end a website to provide services such as Web-Application-Firewalling, (WAF), Caching (CND), and DDOS attack protection (Distributed Denial-of-Service). I’ve activated it for this site, but I only did the free version since this is only a blog after all! Still, very cool technology. Implementing it was a simple 3-step process which really boils down to changing your DNS to point to their many servers.
I found a company called Incapsula that is able to easily front-end a website to provide services such as Web-Application-Firewalling, (WAF), Caching (CND), and DDOS attack protection (Distributed Denial-of-Service). I’ve activated it for this site, but I only did the free version since this is only a blog after all! Still, very cool technology. Implementing it was a simple 3-step process which really boils down to changing your DNS to point to their many servers.
I really like this IFTTT thing. I’ve created some “recipes” to play with and they work pretty well. I created one that allows me to send a SMS with a #r hashtag to IFTTT and the contents are then used to create a reminder note in Microsoft OneNote. I found a couple others of interest including one that monitors for new WordPress posts, and if it contains a specific category or tag, it will post a link to it to my Twitter account. I’ll have to see how well that works.

I started looking at Home automation today and found some great stuff out there. I’m thinking that it would be a could home improvement that won’t break the bank if I’m careful. I really like the idea of thermostat that can be controlled remotely. That would be good when we’re away and we want to adjust it per a unexpected weather change or for our pets if left home (but still watched by our neighbors of course!).
I started looking around and found that Amazon has a great resource page that has tons of information and cool products. I like the Wemo and Nest products but they are very pricy.
The Nest has a very nice looking but somewhat skeuomorphic thermostat that learns and can be controlled remotely. It runs about $250. They also have a very cool smoke/CO2 detector which speaks from all the units in the house which unit has registered smoke or CO2. It has a wave feature to silence the one in the kitchen for those who might burn some toast. These guys run about $120. Pretty pricey for the number I would need.
The Wemo doesn’t appear to have the thermostat, but it does have wall mounted light switches, plugs, and wireless cameras. The light switches pair by acting as a access point to which to connect your phone’s Wemo app, then tell it how to connect to your house access point, then its in business. The app instantly turns the light on and off when in the house and within a half second when elsewhere.
I also learned about a really cool service call If This Then That or IFTTT. It allows you to program just about anything. For example, if I get an email from my wife, I can have it send me an SMS message. But more relevant to home automation, if my favorite team is playing a game, it can change my media room’s lights change colors to my teams colors. Or, if I long-press my Wemo light switch, it can turn on the TV, etc.
I’ll post more later. This is all I have so far!